Operating Instructions for CSP-1750 and CSP-1756 (a.k.a. Penelope)
Kind readers,
Below is a replica of the instructions for operating the CSP-1750 (KA-2) and CSP-1756 (KA-3) also known as Penelope as written for NATO in 1965. The manual has be input using optical character recognition followed by reformatting to network format (HTML.) The formatting does not attempt to preserve the paragraph indenting and font sizes. Please report any obvious typos.
We are still looking for a WW II era instruction book as the use of the device likely evolved during its long lifetime.
Thank you Jerry Proc of HMCS Haida and the Military C&E Museum of Canada for locating and providing a copy of this document.
AMSP 295(B) REGISTER NO. A 6156
REGISTERED DOCUMENT
Downgraded to Unclassified
-See Memo 1000-80/402 (D COMSEC 5-2) 15 Jan 80
INSTRUCTIONS FOR PENELOPE
CYRPTOSYSTEM
OPERATION AND MAINTENANCE OF
CSP 1750 (KA-2) AND CSP 1756 (KA-3)
February 1965
NATO CONFIDENTIAL
February 1965
FOREWORD
1. This is a NATO CONFIDENTIAL registered publication and is issued by the authority of the Communications Electronics Committee of the Standing Group. It shall be transported, stored, safeguarded, and accounted for in accordance with agreed security regulations.
2. This publication will become effective upon receipt and will supersede AMSP 295(A), and AMSP 295(A)-i. At that time AMSP 295(A) and AMSP 295(A)-i will be authorized for destruction. Instructions for the eventual disposal of AMSP 295(B) will be issued at an appropriate time through normal channels.
3. Amendments to this publication will be promulgated by means of a printed or electrically transmitted amendment. Individuals entering such amendments shall so indicate on the "Record of Amendments" page included herein as Page 5.
4. The flyleaf receipts shall be executed in accordance with instructions by those Services requiring their use.
5 HOLDERS OF THIS DOCUMENT ARE WARNED THAT THIS DOCUMENT CONTAINS INFORMATION AFFECTING THE MUTUAL DEFENSE OF THEIR NATION AND OF THEIR ALLIES. THE TRANSMISSION OF THIS DOCUMENT OR THE REVELATION OF ITS CONTENTS IN ANY MANNER TO AN UNAUTHORIZED PERSON IS PROHIBITED.
6. IT IS PERMITTED TO MAKE EXTRACTS FROM THIS PUBLICATION. SUCH EXTRACTS SHALL BE CLASSIFIED NATO CONFIDENTIAL AND ACCOUNTED FOR LOCALLY UNTIL DESTROYED BY BURNING.
7. This publication may not be carried in aircraft for use therein.
NATO CONFIDENTIAL ORIGINAL 1
FLYLEAF RECEIPT
From: ________________________________________
(Title) (Name of Command)
To: ________________________________________
Subject: AMSP 295(B), Register No. ____________________
(Insert No.)
The subject publication has been received and checked against the List of Effective Pages contained therein by:
________________________________________
(Signature, rank, file No.)
|
a. No discrepancies were found.
('X" out a. or b.
as appropriate)
|
b. Discrepancies were found as follows:
|
NOTE: Before executing this form, see paragraph 4 of the Foreword.
|
__________________________________________________________
(Date) (Signature of Commanding Officer)
LIST OF EFFECTIVE PAGES
| Subject Matter |
Effective |
Page Numbers |
|
|
| Front Cover |
ORIGINAL |
Unnumbered (Reverse Blank) |
| Foreword to AMSP 295(B), dated February 1965 |
ORIGINAL |
1 Reverse (Page 2) Blank |
| List of Effective Pages |
ORIGINAL |
3 Reverse (Page 4) Blank |
| Record of Ammendments |
ORIGINAL |
5 Reverse (Page 6) Blank |
| Table of Contents |
ORIGINAL |
7-8 |
| Chapter 1 - General |
ORIGINAL |
9-11 |
| Chapter 2 - CSP 1750 (KA-2) |
ORIGINAL |
12-16 |
| Chapter 3 - CSP 1756 (KA-3) |
ORIGINAL |
17-19 Reverse (Page 20) Blank |
| Chapter 4 - Repair and Maintenance |
ORIGINAL |
21-25 Reverse (Page 26) Blank |
| Chapter 5 - Cryptosecurity |
ORIGINAL |
27 |
| APPENDIX A |
ORIGINAL |
28 |
| APPENDIX B |
ORIGINAL |
29 |
| APPENDIX C |
ORIGINAL |
30-31 |
| APPENDIX D |
ORIGINAL |
32-33 (Reverse Blank) |
NATO CONFIDENTIAL ORIGINAL 3, Reverse (Page 4) Blank
RECORD OF AMENDMENTS
| Identification of Amendment and Reg. No. (if any) |
Date Entered |
By Whom Entered (Signature; Rank or Rate; Name of Command) |
| Suppersession and Quarterly Page Muster Correct |
22-6-65 |
illegible signature |
| Quarterly Muster Page Check Correct |
30-12-65 |
illegible signature |
NATO CONFIDENTIAL ORIGINAL 5, Reverse (Page 6) Blank
|
|
TABLE OF CONTENTS |
|
|
CHAPTER 1 |
|
|
GENERAL |
| Section |
Paragraph |
Subject |
Page Number |
|
101 |
Scope |
9 |
|
102 |
Purpose, Composition and Description of the System |
9 |
|
103 |
Rules for Use |
9 |
|
104 |
Key Card Designator |
9 |
|
105 |
Key List Discriminant |
10 |
|
106 |
Task Element Call Signs |
10 |
|
107 |
Voice Transmission of Encrypted Groups |
10 |
|
108 |
Procedure for Retarding Voice Call Sign Changes |
10-11 |
|
|
CHAPTER 2 |
|
|
OPERATION OF CSP 1750 (KA-2) |
| I |
|
GENERAL |
|
201 |
Description |
13 |
|
202 |
Operating Procedures |
13 |
| II |
|
INSTRUCTIONS FOR ENCRYPTION/DECRYPTION |
|
203 |
Encryption |
13-14 |
|
204 |
Example of Encryption |
14 |
|
205 |
Decryption |
15 |
|
206 |
Example of Decryption |
15 |
|
207 |
Use of the Voice Call Sign Word Square |
15 |
|
208 |
Use of Abbreviated and Phoneticized Voice Call Signs |
15 |
|
209 |
Supplemental Card 32 |
15-16 |
|
|
CHAPTER 3 |
|
|
OPERATION OF CSP 1756 (KA-3) |
| I |
|
GENERAL |
|
301 |
Description |
17 |
| II |
|
INSTRUCTIONS FOR ENCRYPTION/DECRYPTION |
|
302 |
Encryption |
17-18 |
|
303 |
Example of Encryption |
18-19 |
|
304 |
Decryption |
19 |
|
305 |
Example of Decryption |
19 |
|
|
CHAPTER 4 |
|
|
REPAIR AND MAINTENANCE |
| I |
|
CSP 1750 (KA-2) |
|
401 |
Dismantling |
21 |
|
402 |
Lubrication |
21 |
|
403 |
Adjustments |
21-22 |
|
404 |
Replacements |
22 |
|
405 |
Reassembling |
22 |
|
406 |
Spare Parts |
22 |
| II |
|
CSP 1756 (KA-3) |
|
407 |
Repair |
22 |
|
|
CHAPTER 5 |
|
|
CRYPTOSECURITY |
|
|
GENERAL |
|
501 |
Prohibited Practices |
27 |
|
|
APPENDICES |
|
|
APPENDIX A - SAMPLE CARD ENCIPHER |
28 |
|
|
APPENDIX B - SAMPLE CARD DECIPHER |
29 |
|
|
APPENDIX C - SAMPLE TABLE A ENCODE |
30-31 |
|
|
APPENDIX D - SAMPLE TABLE A DECODE |
32-33 |
NATO CONFIDENTIAL ORIGINAL 7&8 (Combined for electronic version.)
CHAPTER 1
GENERAL
101. Scope.- This publication contains information relative to the use of the PENELOPE general cryptosystem and the operation and the maintenance of the two associated crypto devices - CSP 1750 (KA-2) and CSP 1756 (KA-3). It supersedes AMSP 295(A) and AMSP 295(A)-i.
102. Purpose, Composition and Description of the System.
a. Purpose.- The PENELOPE cryptosystem is designed for the encryption of call signs and address groups used on radio circuits, both CW and Voice.
b. Composition.- The system consists of keying material and associated devices designed for encrypting call signs and address groups in the form of 4-character groups, which may be composed of any combination of letters and digits. Encryption will produce an other 4-character group, consisting in this case of any combination of letters, digits and slant (/) signs. The call signs and address groups which are to be encrypted in the system will be found in separate publications.
C. Description.
|
(1) Keying Material. -PENELOPE keying material consists of:
|
(a) A substitution table for changing plain 4-character address groups or call signs to intermediate groups, which are to be further encrypted;
(b) Key cards for use with one of the cryptodevices in encrypting and decrypting the intermediate groups obtained through the substitution table. NOTE: INTERMEDIATE GROUPS ARE NEVER TO BE TRANSMITTED WITHOUT FIRST BEING ENCRYPTED.
Substitution squares and key cards, being complementary, are together known as PENELOPE Key Lists, which are issued under one cover in the AMSP 298 series. Particulars of the editions in force or prescribed for use are promulgated separately and listed in NATO Communication Security Information Memoranda (NAC-SIM).
|
(2) Cryptodevices.-Cryptodevices used in the PENELOPE system are:
|
(a) CSP 1750 (KA-2), a manually operated mechanical device, used in conjunction with key cards to encrypt and decrypt intermediate groups. (Fig. 1.)
(b) CSP 1750 (KA-3), a device using sliding strips, for the same purpose as the CSP 1750 (KA-2), and intended for use whenever the CSP 1750 (KA-2) is inoperable. (Fig. 2.)
|
|
103. Rules for Use.- The circumstances under which the PENELOPE system of call sign encryption is to be used, and the types of transmission to which it is to be applied, will be as directed by appropriate authority. The call signs and address groups to be used for encryption are those listed and specified in the various call sign and address group publications.
104. Key Card Designator.-Each key card contains a 2-character Random Designator which may be sent in a plain text message to signify the key card in effect when the rate of call sign change is slower than daily:
a. To apprise ships joining the force of which key card is in effect:
b. To signal the temporary extension of the effective period of the key card at the discretion of the OTC.
NATO CONFIDENTIAL ORIGINAL 9
105. Key List Discriminant-.Following each 4-character encrypted group, a 5th character must be appended to signify the specific PENELOPE cryptosystem used. This discriminant also serves to distinguish encrypted groups from unencrypted groups. For example, call signs encrypted in the NATO-Wide PENELOPE key list, AMSP 298, would be identified either by appending the slant (/) sign or the suffix P (transmitted . - - . -), to the encrypted group, contingent upon the key card employed.
106. Task Element Call Signs.- There are two methods of deriving encrypted task element call signs. First, the Task Unit call sign is encrypted in the prescribed manner with the appropriate key list discriminant being appended as the 5th character. The unencrypted number of the Task Element is then added as the 6th and final character of the encrypted call sign. An alternative method is to encrypt a task element call sign which has been assigned by the Officer in Tactical Command (OTC) from the block of calls provided in the appropriate Task Organization Call Sign Publication. The latter method is used when the OTC desires to conceal the existence of Task Elements.
107. Voice Transmission of Encrypted Groups.- Any encrypted call sign, address group or other group may be transmitted phonetically on voice circuits. Furthermore, if desired, encrypted call signs and address groups may be changed to a pair of words for voice transmission by use of a word square which is included with the appropriate PENELOPE keying material.
108. Procedure for Retarding Voice Call Sign Changes.
a. General.- A procedure known as MISFIT has been devised for retarding voice call sign changes when a force is engaged in action at a time scheduled for a call sign change. Implementation of MISFIT Procedure merely continues the use of voice call signs already in effect past the time scheduled for their supersession; it has no effect on the supersession of RATT/CW call signs. Thus, when MISFIT is declared and the time scheduled for normal call sign change is reached, AMSP 298 key card supersession will take place, new call signs (CW/RATT and voice) will be derived, and all but the newly derived voice call signs put in use. (The derivation of new voice call sign may be delayed until the time for recission of MISFIT is known.) As long as MISFIT is in effect, the voice call signs already in use, derived by means of the superseded key card, will remain in effect.
b. Description and Instructions. - The terms "MISFIT" and "CHARTER" have been selected to mean "Implement" and "Rescind" MISFIT Procedure, respectively. They are used in the following manner:
(1) MISFIT. When it is considered expedient to retard a voice call sign change, the OTC may do so by ordering transmission of the term "MISFIT", followed by the random designator (e.g., DH) of the AMSP 298 daily-changing key card in use at the time, to all Force units using voice radio communications. This order will inform all units concerned that the voice call signs derived by means of the key card designated will remain in use until further notice. Transmission of the order will be by the most expeditious means possible, in accordance with standard signal and communications procedures, and with the security restrictions in Paragraph d, below. (It is assumed that MISFIT procedure will normally be ordered into use over the voice radio circuits it will affect.)
EXAMPLE: A force is engaged by the enemy at 2330Z, and has a call sign change scheduled for 0001Z. The Force OTC feels that conducting the call sign change as scheduled on the Force's voice radio circuits will be deleterious to his tactical control. AMSP 298 key card "DH" is in use by the units of his Force. The OTC orders the following transmission made to all Force units concerned:
MISFIT DELTA HOTEL
As transmitted, this order means "continue using voice call signs encrypted by means of AMSP 298 daily-changing key card "DH" until further notice."
NATO CONFIDENTIAL ORIGINAL 10
(2) CHARTER.-When the situation requiring retardation of the voice call signs change has passed, replacement of the superseded voice call sign will be effected as soon as possible. The OTC may accomplish this by ordering transmission to units concerned of the term "CHARTER", followed by the designation of the effective AMSP 298 key card by which the new voice call signs will be derived, and a time (rendered in Numeral Code) indicating when that key card is to be put in use.
EXAMPLE: The action which caused the OTC to order MISFIT has ended at 0700Z. The OTC wishes to allow time for regrouping before changing call signs, so decides to wait until 0800Z to put the deferred key card (e.g.. "DZ") into effect. The OTC orders the following transmission made to all Force units concerned:
CHARTER DELTA ZULU NUCO ALFA KILO FOXTROT VICTOR LIMA KILO UNUCO (0800Z)
As transmitted, this order means "Change to call signs encrypted by means of AMSP 298 daily-changing key card "DZ" at 0800Z".
c. Promulgation.- The OTC will ensure simultaneous promulgation of MISFIT procedure on all voice radio circuits under his control.
d. Security.- Ordering MISFIT procedure into effect in the manner described above before engagement in action has occurred could betray to opposing forces that an operation is impending. Therefore, any orders issued prior to engagement in action which indicate that MISFIT procedure is to be implemented will be afforded physical or cryptographic security in their transmission.
NATO CONFIDENTIAL ORIGINAL 11
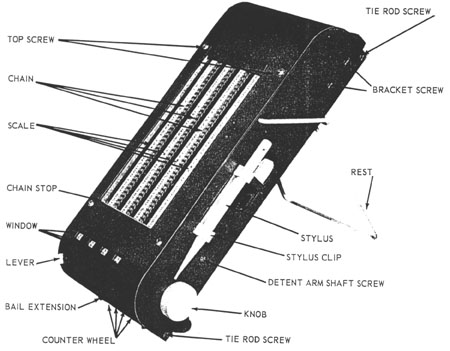
Figure 1.-CSP 1750 (KA-2)
NATO CONFIDENTIAL ORIGINAL 12
CHAPTER 2
OPERATION OF CSP 1750 (KA-2)
SECTION I-GENERAL
201. Description.
a. CSP 1750 is a manually operated cipher device which is employed in enciphering and deciphering 4-character groups for which intermediate groups have been substituted.
b. The cipher device is of metal construction. On its surface are four columns of characters with a movable chain beside each column. Below the four columns of characters are four windows in which appear the counter numbers for each column. A metal stylus is attached in brackets on the side of the device for use in moving the chains.
202. Operating Procedures.
a. Zeroizing.- Before beginning encipherment or decipherment the cipher device must be zeroized, i.e., each of the four counters must read zero (00). Zeroizing is performed by holding down the lever at the lower left corner of the device and by turning the knob on the lower right side toward the operator (counterclockwise). When the knob locks and zero (00) appears on the counters, the cipher device is correctly zeroized.
b. Registering Characters. - To register a character, insert the stylus in the chain link opposite the desired character and perpendicular to the face of the device. Pull downward until the stylus reaches the metal bar below the columns of characters; the total will appear on the counter below the column used.
SECTION II-INSTRUCTIONS FOR ENCRYPTION/DECRYPTION
203. Encryption.
a. Encrypted call signs/address groups are derived from the plain groups listed in the applicable publications.
b. Using the plain 4-character group, an intermediate group is derived from the Encode section of Table A. The intermediate group derived from Table A is encrypted using the appropriate key card (1 through 31) to produce daily changing encrypted call signs or address groups or using "Supplemental Card 32"" to produce monthly changing call signs (see par. 209 for instructions pertaining to card 32). Encrypted 4-character groups may be transmitted on any type circuit. For voice transmissions, the encrypted group may be spoken phonetically or converted to a pair of words by means of the Voice Call Sign Word Square in the appropriate key list. (See par. 207.)
c. The first two characters of a 4-character group are called the first digraph and the last two characters are called the second digraph.
d. The plain group is converted to an intermediate group by a process of digraph for digraph substitution in Table A.
e. Using the first character of the first digraphs the row coordinate and the second character of the first digraph as the column coordinate on the appropriate table, locate the cell which lies at the intersection of the two coordinates. The substitute for the first digraph is found in the UPPER HALF of this cell. The substitute for the second digraph is found in the LOWER HALF of the cell located at the intersection of the second digraph coordinates. For example, in the 4-character group ABRD, AB is the first digraph and RD is the second digraph. The substitute for AB is located in the UPPER HALF of the cell at the intersection
NATO CONFIDENTIAL ORIGINAL 13
of Row A with Column B. The substitute for RD is located in the LOWER HALF of the cell at the intersection of Row R with Column D. The intermediate group is thus obtained.
f. Zeroize the CSP 1750. (See par. 202a.)
g. Using the ENCIPHER side of the effective key card, locate the first character of the intermediate group in the bold-face column under the heading "1st CHAR." To the right of the character so located are four characters.
h. Register the first of these four characters on the first chain of the device, the second character on the second chain, and the third and fourth characters on the third and fourth chains respectively.
i. Locate the second, third, and fourth characters of the intermediate group in the bold-face columns under the headings "2nd CHAR," "3rd CHAR," "4th CHAR," and register the four characters opposite each bold-face character in the first, second, third, and fourth columns of the cipher device, as described in h.above. The totals of all the characters registered will now appear on the counters.
j.At the right-hand side of the key card is a column of numbers, 00 through 36, together with four ENCIPHER columns headed 1, 2, 3, and 4. Locate the number in the column of numbers which corresponds to the total shown on the first counter. Locate the character in column 1 which is opposite that number. In column 2 locate the character opposite the total shown on the second counter. In column 3 locate the character opposite the total shown on the third counter. In column 4 locate the character opposite the total shown on the fourth counter. The order of these characters must be the same as the order of the totals on the counters reading from left to right. The four characters located in this manner constitute the enciphered call sign.
k. The unencrypted key list discriminant (see par. 105) is suffixed to the 4-character encrypted group as a means of identifying the key list used to accomplish the encryption.
204. Example of Encryption.
a. In ACP 113, the call sign L4Y4 is obtained for the U. S. Ship, Franklin D. Roosevelt.
b. From Sample TABLE A ENCODE on page 30 an intermediate group is obtained. The digraph AG is found in the UPPER HALF of the cell at the intersection of Row L and Column 4. The digraph 71 is found in the LOWER HALF of the cell at the intersection of Row Y and Column 4. The intermediate group AG71 is now formed.
c. Zeroize the cipher device.
d. Refer to the ENCIPHER side of the sample key card on page 28. In the "1st CHAR" column opposite A (first character of the intermediate group) ABLS is found.
e. Register A in the first chain of the device, B in the second chain, L in the third chain, S in the fourth chain. The counters at the bottom of the device now read 36-35-25-18.
f. In the &"2nd CHAR" column of the sample key card opposite G (second character of the intermediate group) locate NIS5. Register these characters in the first, second, third and fourth chains of the device. The counters now read 22-26-06-23.
g. In the "3rd CHAR" column opposite 7 (third character of the intermediate group) locate and register 4/lY. The counters now read 28-36-15-35.
h. In the "4th CHAR" column opposite 1 (fourth character of the intermediate group) locate register OZlE. The counters now read 13-10-24-30.
i. Using the four ENCIPHER columns on the key card, find the characters opposite 13-10-24-30 in columns 1, 2, 3, and 4, respectively. The result is G6N7, which is the enciphered call sign.
NATO CONFIDENTIAL ORIGINAL 14
205. Decryption.
a. Use the enciphered call sign as received deleting the key list discriminant and the Task Element number, if included.
b. Zeroize the cipher device.
c. Proceed through the steps outlined in paragraphs 203g through 203j using the DECIPHER side of the effective key card and the enciphered call sign to obtain the intermediate group.
d. With the intermediate group thus obtained turn to the DECODE side of Table A and proceed through the steps outlined in paragraph 203e to obtain the plain call sign.
206. Example of Decryption.
a. Use the enciphered call sign G6N7.
b. Zeroize the cipher device.
c. Refer to the DECIPHER side of the sample key card on page 29. In the "1st CHAR"' column opposite G (first character of enciphered call sign) locate the four characters XXXX.
d. Register X on all four chains of the device. The counters at the bottom of the device now read 13-13-13-13.
e. In the "2nd CHAR" column of the key card, opposite 6 (second character of the enciphered call sign) locate /TDF. Register these characters in the first, second, third, and fourth chains of the device. The counters now read 23-30-09-07.
f. In the "3rd CHAR"' column opposite N (third character of the enciphered call sign) locate and register M79L. The counters now read 10-33-10-32.
g. In the "4th CHAR" column opposite 7 (fourth character of the enciphered call sign) locate and register GUE8. The counters now read 03-12-05-34.
h. Using the four DECIPHER columns on the key card, find the characters opposite 03-12-05- 34 in columns 1, 2, 3 and 4, respectively. The result is AG7l, which is the intermediate group.
i. Refer to TABLE A DECODE, at the intersection of Row A with Column G, the digraph L4 is found. At the intersection of Row 7 with Column 1, the digraph Y4 is found. Combining these, the plain call sign L4Y4 is recovered.
207. Use of the Voice Call Sign Word Square.-When word call signs are used on voice circuits, the 4-character encrypted call signs can be converted to a pair of words by means of a word square provided in the appropriate key list. The encrypted call sign is divided into two digraphs. The first and second characters in the first digraph are used as row and column coordinates, respectively, to locate a word in the UPPER HALF of the cell. Similarly, the characters of the second digraph are used to locate a word in the LOWER HALF of the indicated cell. These two words may be used together as a secure voice call sign. Since the words in the Voice Call Sign Word Square are arranged alphabetically, the encrypted call sign can be recovered by reversing the process described above.
208. Use of Abbreviated and Phoneticized Voice Call Signs.- Any encrypted call sign or address group may be transmitted phonetically on voice circuits. At the option of OTC's the use of abbreviated and phoneticized voice call signs may be ordered. After initial communication has been established and if no confusion with other stations will result, the first two (or three, if necessary) letters of the encrypted CW call sign will be used for the voice call sign.
209. Supplemental Card 32.-Each edition of AMSP 298 contains a supplemental key card entitled "Supplemental Card 32'". This card is used to derive monthly changing encrypted call signs for individual merchant ships in wartime or during Exercises and for war ships
NATO CONFIDENTIAL ORIGINAL 15
simulating merchant ships during Exercises. Encryption and decryption procedures are the same as described in Chapters 2 and 3 of this publication. This card will be used only for the purpose stated above unless authorized by appropriate authority for additional use.
Note: CALL SIGNS ENCRYPTED THROUGH CARD 32 MUST CONTAIN THE KEY LIST DISCRIMINANT P, RATHER THAN (/).
NATO CONFIDENTIAL ORIGINAL 16
CHAPTER 3
OPERATION OF CSP 1756 (KA-3)
SECTION I-GENERAL
301. Description.
a. CSP 1756 is a cipher device designed for the same purpose as the CSP 1750 and intended for use whenever CSP 1750 is not available.
b. The device is a wooden board with a fixed plastic strip at the top, another fixed plastic strip at the bottom, and three grooved channels in the center, each containing a sliding strip. The plastic strip at the top is marked with an alphabet-numeral sequence consisting of a normal alphabet, a slant sign, and the numbers one through zero. The plastic strip at the bottom is marked with a numeral sequence consisting of a series of numbers from 00 to 36 in reverse order. Each of the three sliding strips is marked with a normal alphabet, a slant sign, the numbers one through zero, a vertical, black line, and the same sequence of characters repeated.

Figure 2. -CSP 1756 (KA-3)
SECTION II-INSTRUCTIONS FOR ENCRYPTION/DECRYPTION
302. Encryption.
a. Write the four characters of the plain call sign vertically on a work sheet.
b. Using the ENCIPHER side of Table A proceed through the steps outlined in paragraph 203e to obtain the intermediate group, which is then written vertically on the work sheet to the right of the plain call sign.
c. Refer to the ENCIPHER side of the effective key card. Locate the first character of the intermediate group in the bold-face column under the heading "1st CHAR". To the right of the character so located are four characters. Write these four characters on the work sheet horizontally and to the right of the first character of the intermediate group.
d. Locate the second character of the intermediate group in the bold-face column under the heading "2nd CHAR", lining up the equivalent four characters immediately under the four characters previously entered on the work sheet.
e. In the same manner, line up the four equivalent characters for the third and fourth characters of the intermediate group located in the bold-face columns under the heading "3rd CHAR" and "4th CHAR'". The equivalents for the characters composing the intermediate group are now arranged in four rows on the work sheet.
NATO CONFIDENTIAL ORIGINAL 17
f. In the fixed alphabet-numeral sequence at the top of the cipher device locate the first character in the first column of the four rows listed on the work sheet, and slide the first movable strip so that 0 falls immediately below this character.
g. On the first movable strip locate the second character in Column 1 of the work sheet, and slide the second movable strip so that 0 falls immediately below this character.
h. On the second movable strip locate the third character in Column 1 of the work sheet, and slide the third movable strip so that 0 falls immediately below this character.
i. On the third movable strip locate the fourth character in Column 1 of the work sheet, and note the number appearing immediately below this character in the fixed numeral sequence.
j. In the ENCIPHER column of the key card locate the number found in i above. The character appearing in column 1 opposite this number is the first character of the enciphered call sign.
k. Repeat the steps described in f through j above for the characters in the second, third, and fourth columns of the work sheet, using ENCIPHER columns 2, 3, and 4, respectively of the key card. The results are the second, third, and fourth characters of the enciphered call sign.
l. The unencrypted key list discriminant (see par. 105) is suffixed to the 4-character encrypted group as a means of identifying the key list used to accomplish the encryption.
m. If the call sign is to be transmitted over a voice circuit see paragraphs 207 and 208.
303. Example of Encryption.
a. Use the plain call sign L4Y4 writing it vertically on the work sheet:
L
4
Y
4
b. Following the procedure in paragraph 204b, determine the intermediate group and write it vertically to the right of the plain call sign:
L A
4 G
Y 7
4 1
c. Opposite each character of the intermediate group write the equivalent four characters from the "1st CHAR", "2nd CHAR", "3rd CHAR", and "4th CHAR" columns of the ENCIPHER side of the effective key card. The equivalents for the four characters of the intermediate group are now arranged in four columns and four rows on the work sheet:
L A ABLS
4 G NIS5
Y 7 4/lY
4 1 OZlE
d. Using the first column of the work sheet (AN4O) locate the first character (A) on the fixed alphabet-numerical sequence at the top of the cipher device. Slide the first movable strip so that 0 falls below A of the fixed alphabet-numerical sequence. Slide the second movable strip so that 0 falls below N of the first movable strip. Slide the third movable strip so that 0 falls below 4 of the second movable strip. Locate O on the third movable strip and note the number below it in the fixed numeral sequence at the bottom of the cipher device, which is 13.
e. Following the procedure in d above, slide the strips in accordance with the second, third, and fourth columns of the work sheet and note the resulting numbers: 10-24-30.
NATO CONFIDENTIAL ORIGINAL 18
f. Using the four ENCIPHER columns on the key card, find the characters opposite 13-10-24-30 in columns 1, 2, 3, and 4, respectively. The result is G6N7, which is the enciphered call sign.
304. Decryption.
a. Write the four characters of the enciphered call sign vertically on a work sheet. (Disregard the key list discriminant suffixed to the enciphered call sign.)
b. Proceed through the steps described in paragraphs 302c through 302k using the DECIPHER side of the effective key card and the enciphered call sign, to obtain the intermediate group.
c. With the intermediate group thus obtained turn to the DECODE side of Table A and proceed through the steps outlined in paragraph 201e to obtain the plain call sign.
305. Example of Decryption.
a. Use the enciphered call sign G6N7 writing it vertically on the work sheet.
G
6
N
7
b. Opposite each character of the call sign, write the equivalent four characters from the "1st CHAR", "2nd CHAR" "3rd CHAR", and "4th CHAR'" columns of the DECIPHER side of the effective key card. The equivalents for the four characters of the call sign are now arranged in four columns on the work sheet:
G XXXX
6 /TDF
N M79L
7 GUE8
c. Using the first column of the work sheet X/MG, locate the first character (X) on the fixed alphabet-numerical sequence at the top of the cipher device. Slide the first movable strip so that 0 falls below X of the fixed alphabet-numerical sequence. Slide the second movable strip so that 0 falls below / of the first movable strip. Slide the third movable strip so that 0 falls below M of the second movable strip. Locate G on the third movable strip and note the number below it in the fixed numeral sequence at the bottom of the device, which is 03.
d. Following the procedure in c above, slide the strips in accordance with the second, third, and fourth columns of the work sheet, and note the resulting numbers: 12-05-34.
e. Using the four DECIPHER columns on the key card, find the characters opposite 03-12-05-34 in columns 1, 2, 3, and 4, respectively. The result is AG7l which is the intermediate group.
f. Refer to Table A DECODE. At the intersection of Row A with Column G the digraph L4 is found in the UPPER HALF of the cell. At the intersection of Row 7 with Column 1 the digraph Y4 is found in the LOWER HALF of the cell. Combining these digraphs the plain call sign L4Y4 is recovered.
NATO CONFIDENTIAL ORIGINAL 19
CHAPTER 4
REPAIR AND MAINTENANCE
SECTION 1-CSP 1750 (KA-2)
401. Dismantling.
a. To dismantle CSP 1750 (KA-2), proceed as follows:
(1) Remove (1) finger piece, (2) top of the device, and (3) bottom of the device.
(2) Back out the adjusting screws until the chains are slack enough to be slipped from the pulleys.
(3) Remove, in this sequence, (1) tie rods, (2) support bracket, (3) chain stop, (4) chain guide, (5) scales, (6) chains, (7) counter wheel shaft, and (8) counter wheels.
(4) Unhook the stop arm bail spring and the detent arm springs.
(5) Release the detent arm shaft.
(6) Remove (1) stop arm bail, (2) detent arms and (3) spring shaft.
402. Lubrication.
a. Use any light grade lubricating oil and lubricate the following parts as frequently as usage of the equipment requires:
(1) Reset pin, one drop.
(2) Detent arm roller, one drop.
(3) Detent arm hub, one drop.
(4) Pulley stud, one drop.
(5) Counter wheel shaft, several drops along the longitudinal groove.
403. Adjustments.
a. Remove top and bottom of the device.
b. With the counters zeroized, the rear edge of the reset arm fingers should clear the stop pins sufficiently to permit the arms to be fully seated on the pins. To adjust, bend the reset arm fingers using duckbill pliers or a similar tool. To facilitate this adjustment, the chains may be slipped from the sprockets.
c. With the reset arms fully seated on the pins, the bail extension should rest on the bushing. To adjust, grasp the bail with long nose pliers near the bail extension and hold as immovable as possible while bending the bail extension toward or away from the bushing.
d. Each pulley and the corresponding chain should be in alignment. To adjust a pulley that is in the path of but not parallel to the chain, align by twisting the tension arm. If a pulley is parallel to but not in line with the path of the chain, loosen the tension arm bracket screws and position the arm. Tighten the screws.
e. The counter wheel characters should be centered in their respective windows. In order to adjust, the counter wheels should be removed from the device. Loosen the three sprocket screws and rotate the sprocket slightly. Tighten the screws and replace the counter wheels. Adjust the chain tension.
f. Proper chain tension may be obtained by advancing the adjusting screws until all slack has been taken up and the chain feels taut. Check with finger pressure against the under part of the chain. Excessive tension will cause the device to operate stiffly and may stretch or break the chain.
NATO CONFIDENTIAL ORIGINAL 21
g. The centers of the scale characters should be opposite the centers of respective chain links. To adjust, loosen the scale and chain stop screws and position the scales. Tighten the screws.
h. The stop arm bail spring tension is measured as follows: Apply an 8-ounce push scale perpendicular to the end of the bail extension and push down. It should require approximately 1-1/2 ounces to start the bail extension moving.
i. The detent arm spring tension is measured as follows: Hook a 32-ounce spring scale over the detent arm at the spring hole and pull in line with the spring. It should require approximately 30 ounces to move the detent arm roller away from the sprocket.
404. Replacements.
a. To replace or clean a reset pin, remove the counter wheel from the device. Remove the sprocket, unhook the reset spring and lift the reset pin from the hub. When replacing the sprocket on the hub, note that the relative position of the stop pin and the counter wheel guide hole are maintained.
b. To replace a knob, remove the shaft and drive the knob pin from the assembly. Replace the knob and insert a new pin. Peen the end of the pin and replace the shaft.
c. To facilitate removal of a chain, first reduce the chain tension. Open a link by using long nose pliers and pull the chain from the device. When replacing the chain, be sure that the open end of the link is toward the chain stop. Rejoin the ends and adjust the chain tension.
405. Reassembling.
a. CSP 1750 (KA-2) is reassembled by reversing the procedure for dismantling described in paragraph 401.
b. All parts should be wiped clean before reassembling.
406. Spare Parts.- Spare parts as listed in page 25 to be used as replacements may be ordered from the Signal Officer of the appropriate Supreme Allied Commander through proper channels.
SECTION II-CSP 1756 (KA-3)
407. Repair.- Because of the simplicity of its design, the only attention this device should require is replacement of plastic alphabet or number strips. Before replacing a strip, the surface of the device should be cleaned. Use a liquid cement or other similar water-proof adhesive to cement the strip to the device. It should be noted that the "A" of the top strip is cemented directly above the "36" of the bottom strip.
NATO CONFIDENTIAL ORIGINAL 22
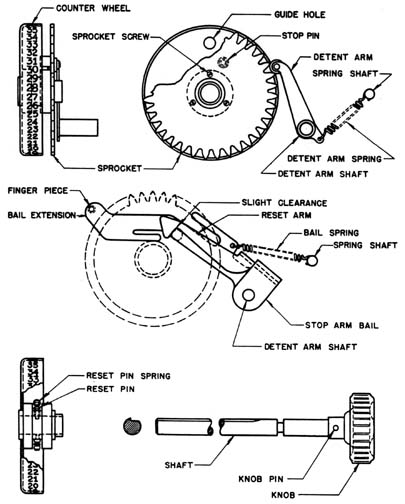
Figure 3
NATO CONFIDENTIAL ORIGINAL 23
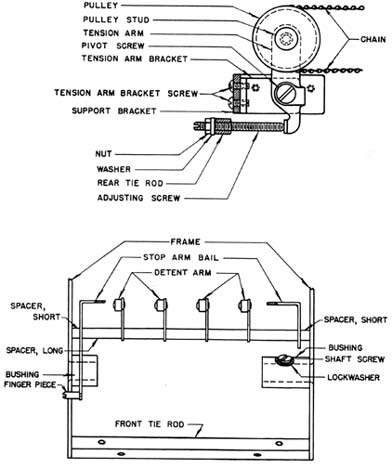
Figure 4
NATO CONFIDENTIAL ORIGINAL 24
PARTS LIST
| Part Name |
Quantity |
Description |
Part No. |
| Adjusting Screw |
4 |
8-32 x 1.500 |
C29 |
| Bail Spring |
1 |
45 turns length 1.106 |
C56 |
| Bottom |
1 |
|
MC4 |
| Bottom Screw |
4 |
straight side binding head 5-40 x .300 |
C5 |
| Chain |
4 |
|
C25 |
| Chain Guide |
1 |
|
C39 |
| Chain Stop |
1 |
|
C38 |
| Chain Stop Screw |
5 |
flat head 5-40 x .312 |
C38A |
| Counter Wheel |
4 |
|
MC 11 |
| Counter Wheel Shaft |
1 |
|
C13 |
| Counter Wheel Shaft Screw |
1 |
6-32 thread |
C16 |
| Detent Arm |
4 |
|
MC |
18 |
| Detent Arm Shaft |
1 |
|
C22 |
| Detent Arm Shaft Screw |
2 |
flat head 5-40 x .250 |
C23** |
| Detent Arm Spring |
4 |
25 turns length 1.000 |
C24A |
| Finger Piece |
1 |
5-40 thread |
C58A |
| Foot |
2 |
rubber |
C6 |
| Frame |
1 |
|
2MC40 |
| Knob |
1 |
plastic |
MC 14 |
| Knob Pin |
1 |
|
C15 |
| Lock Washer |
1 |
Shakeproof |
C17 |
| Nut |
4 |
hex 8-32 |
C29A |
| Reset Pin |
4 |
|
C50 |
| Reset Pin Spring |
4 |
175 turns length 2.616 |
C51 |
| Rest |
1 |
|
C59 |
| Scale |
4 |
|
C35 |
| Scale Screw |
5 |
round head 5-40 x .225 |
C36* |
| Spacer, long |
1 |
OD .312 ID .196 .810 long |
C58 |
| Spacer, short |
2 |
OD .312 ID .196 .115 long |
C57 |
| Spring Shaft |
1 |
|
C24 |
| Spring Shaft Screw |
2 |
flat head 5-40 x .250 |
C24B** |
| Sprocket |
4 |
|
MC48 |
| Sprocket Screw |
12 |
fillister head 2-56 x .218 |
C55 |
| Stop Arm Bail |
1 |
|
MC54 |
| Support Bracket |
1 |
|
C33 |
| Support Bracket Screw |
4 |
flat head 5-40 x .250 |
C34** |
| Stylus |
1 |
|
C60 |
| Stylus Clip |
2 |
|
C61 |
| Stylus Clip Screw |
2 |
round head 2-56 x.125 |
C62 |
| Tension Arm (with pulley) |
4 |
|
MC30 |
| Tension Arm Bracket |
4 |
|
C32 |
| Tension Arm Bracket Screw |
8 |
round head 5-40 x .225 |
C34A* |
| Tension Arm Pivot Screw |
4 |
5-40 thread |
C31 |
| Tie-rod front |
1 |
|
C42F |
| Tie-rod rear |
1 |
|
C42R |
| Tie-rod Screw |
4 |
flat head 5-40 .250 |
C43** |
| Top |
1 |
|
MC1 |
| Top Screw |
8 |
round head 5-40 x .225 |
C2* |
| Washer |
4 |
OD .375 ID .170 .062 thick |
C34B |
* IDENTICAL
** IDENTICAL
NATO CONFIDENTIAL ORIGINAL 25, Reverse (Page 26) Blank
CHAPTER 5
CRYPTOSECURITY
501. Prohibited Practices.- The following practices are considered to be dangerous and are prohibited:
a. The association of a PENELOPE encrypted call sign or address group with its corresponding plain call sign or address group.
b. Linkage of encrypted PENELOPE call signs or address groups having the same underlying signification but encrypted during different cryptoperiods.
c. Transmission in the clear of any intermediate group derived from the Table A.
d. Transmission in the clear of any 4-character group from the ENCIPHER Table of the applicable key list.
NATO CONFIDENTIAL ORIGINAL 27
APPENDIX A
SAMPLE CARD
ENCIPHER
RANDOM
DESIGNATOR: D9
DAY OF MONTH-CARD NO: 02
|
|
|
|
|
|
|
|
|
ENCIPHER |
|
1ST CHAR |
|
2ND CHAR |
|
3RD CHAR |
|
4TH CHAR |
|
1 2 3 4 |
| A |
ABLS |
A |
5JQ0 |
OA |
NKU1 |
A |
0000 |
00 |
MIDZ |
| B |
UE32 |
B |
WIRE |
B |
GX2N |
B |
HDJO |
01 |
JH46 |
| C |
WIQ3 |
C |
FYXS |
C |
/HVQ |
C |
W3AT |
02 |
X8QC |
| D |
VGEK |
D |
V3NH |
D |
E6ZJ |
D |
LFOD |
03 |
NEY9 |
| E |
JTIE |
E |
U5JK |
E |
DSFH |
E |
FCZB |
04 |
ZIRD |
| F |
4YB7 |
F |
HUSM |
F |
LTRX |
F |
BAUM |
05 |
8RE3 |
| G |
74AQ |
G |
NIS5 |
G |
IO5R |
G |
IWBC |
06 |
Y4O0 |
| H |
FL8C |
H |
E/TV |
H |
R3/9 |
H |
GVR/ |
07 |
AZ0N |
| I |
TCRJ |
I |
0000 |
I |
5DK/ |
I |
47K8 |
08 |
O37B |
| J |
CF9T |
J |
2PEX |
J |
YQSM |
J |
RIDF |
09 |
QLFO |
| K |
GNJV |
K |
OGW2 |
K |
0000 |
K |
26/V |
10 |
W6W4 |
| L |
86M9 |
L |
RA8T |
L |
9WQ8 |
L |
DBEZ |
11 |
59A/ |
| M |
1SCN |
M |
3NIU |
M |
XC9K |
M |
1N87 |
12 |
929K |
| N |
S/NP |
N |
JQCG |
N |
J2OT |
N |
7QX9 |
13 |
GXMX |
| O |
DHKB |
O |
9B6C |
O |
PBX5 |
O |
Q/LR |
14 |
0DIP |
| P |
ZOPM |
P |
ZV36 |
P |
75N4 |
P |
9RHL |
15 |
K/5A |
| Q |
IR7W |
Q |
T7FN |
Q |
VL6G |
Q |
KXWP |
16 |
/WIR |
| R |
P5GH |
R |
B6H4 |
R |
FJIL |
R |
Y4V6 |
17 |
H5XE |
| S |
KVUX |
S |
QC4W |
S |
CEWF |
S |
3O5J |
18 |
DV8M |
| T |
2UO6 |
T |
7FYI |
T |
8I76 |
T |
/5FI |
19 |
LOK2 |
| U |
/QlS |
U |
MKO8 |
U |
HALP |
U |
ZMNU |
20 |
U7G8 |
| V |
SAFI |
V |
/T73 |
V |
OYD3 |
V |
89PX |
21 |
SMLQ |
| W |
LX6F |
W |
A8D7 |
W |
M7AZ |
W |
EU7N |
22 |
PUCJ |
| X |
Q7S/ |
X |
LMKA |
X |
29YU |
X |
VKI5 |
23 |
7T25 |
| Y |
3W/O |
Y |
8D2F |
Y |
SGJA |
Y |
MYG2 |
24 |
CJNV |
| Z |
EJWU |
Z |
GW1P |
Z |
WZPI |
Z |
XL3H |
25 |
VKPH |
| / |
98YR |
/ |
1RA/ |
/ |
lVES |
/ |
TJYS |
26 |
FCHW |
| l |
HPVD |
l |
KOGD |
l |
U8ME |
l |
OZ1E |
27 |
IYJ1 |
| 2 |
YMD4 |
2 |
XZVB |
2 |
6R42 |
2 |
5PCW |
28 |
ENTT |
| 3 |
R941 |
3 |
C4L1 |
3 |
Z4BO |
3 |
NG9Q |
29 |
4F/U |
| 4 |
NITG |
4 |
S9BQ |
4 |
B1CD |
4 |
AS2Y |
30 |
6Q67 |
| 5 |
62Z8 |
5 |
IS9J |
5 |
ANTB |
5 |
U2QG |
31 |
2PVF |
| 6 |
MZHY |
6 |
YXZ9 |
6 |
KF8V |
6 |
S164 |
32 |
T0Ul |
| 7 |
0000 |
7 |
6HUL |
7 |
4/1Y |
7 |
JE41 |
33 |
RSBI |
| 8 |
O35Z |
8 |
O2PY |
8 |
QPG7 |
8 |
685K |
34 |
BB3G |
| 9 |
BDXA |
9 |
PE/Z |
9 |
TU3C |
9 |
CTMA |
35 |
1AZS |
| 0 |
XK2L |
0 |
4LMR |
0 |
3MHW |
0 |
PHT3 |
36 |
3GSY |
CHECK CALL: A B C D - 5 Q 0 U
NATO CONFIDENTIAL ORIGINAL 28
APPENDIX B
SAMPLE CARD
DECIPHER
RANDOM
DESIGNATOR: D9
DAY OF MONTH-CARD NO: 02
|
|
|
|
|
|
|
|
|
DECIPHER |
|
1ST CHAR |
|
2ND CHAR |
|
3RD CHAR |
|
4TH CHAR |
|
1 2 3 4 |
| A |
3333 |
A |
B6NU |
A |
Z48X |
A |
V2U9 |
00 |
7IKA |
| B |
CCCC |
B |
C4UM |
B |
DS48 |
B |
2MZ7 |
01 |
2A12 |
| C |
MMMM |
C |
KOCW |
C |
OY6K |
C |
84Y/ |
02 |
6VDT |
| D |
SSSS |
D |
W1MA |
D |
0000 |
D |
6YMQ |
03 |
AD3X |
| E |
IIII |
E |
7FPX |
E |
5DZU |
E |
TWIZ |
04 |
PSNO |
| F |
KKKK |
F |
HUSJ |
F |
1V5W |
F |
FR93 |
05 |
4X7D |
| G |
XXXX |
G |
A8G2 |
G |
QP3J |
G |
CIRO |
06 |
9ZVH |
| H |
TTTT |
H |
9B3H |
H |
KFBM |
H |
L98W |
07 |
URLF |
| I |
JJJJ |
I |
0000 |
I |
WZUG |
I |
DLXT |
08 |
8T9N |
| J |
9999 |
J |
MKQG |
J |
J2V5 |
J |
OHPA |
09 |
JJEK |
| K |
VVVV |
K |
LMJO |
K |
R3J1 |
K |
YABN |
10 |
M2JZ |
| L |
RRRR |
L |
1RK8 |
L |
PBM2 |
L |
EO3Y |
11 |
R4G6 |
| M |
0000 |
M |
PEAT |
M |
XCAY |
M |
STCU |
12 |
OG03 |
| N |
7777 |
N |
ISZB |
N |
M79L |
N |
3P5B |
13 |
T5AG |
| O |
2222 |
O |
RAOD |
O |
4/IC |
O |
1JT2 |
14 |
X8TL |
| P |
0000 |
P |
FYEZ |
P |
LTS4 |
P |
W5/D |
15 |
ZOYP |
| Q |
1111 |
Q |
GWLR |
Q |
8ICA |
Q |
PKVF |
16 |
Y0SI |
| R |
DDDD |
R |
5J8C |
R |
6RFB |
R |
UZO4 |
17 |
3PMU |
| S |
PPPP |
S |
D21E |
S |
ANQR |
S |
BFLJ |
18 |
HEU5 |
| T |
EEEE |
T |
NIX9 |
T |
IOEN |
T |
I/OH |
19 |
F9XO |
| U |
QQQQ |
U |
OG41 |
U |
E6KP |
U |
HXKC |
20 |
V1WQ |
| V |
LLLL |
V |
S9V6 |
V |
FJ17 |
V |
MBD1 |
21 |
KCPE |
| W |
//// |
W |
U59Q |
W |
/HOE |
W |
K62R |
22 |
NWH4 |
| X |
8888 |
X |
XZT3 |
X |
TUG/ |
X |
X861 |
23 |
1748 |
| Y |
4444 |
Y |
JQ64 |
Y |
75WT |
Y |
ACFE |
24 |
l/ZM |
| Z |
6666 |
Z |
3NYS |
Z |
8179 |
Z |
0000 |
25 |
5BBC |
| / |
UUUU |
/ |
V3FI |
/ |
HAY6 |
/ |
ZDHS |
26 |
BL/J |
| l |
BBBB |
l |
6HI5 |
l |
U8XH |
l |
J3WM |
27 |
QUFY |
| 2 |
FFFF |
2 |
YX/V |
2 |
NKP3 |
2 |
RQ7P |
28 |
GF2B |
| 3 |
AAAA |
3 |
2PR/ |
3 |
CENO |
3 |
5VGL |
29 |
D389 |
| 4 |
HHHH |
4 |
4LSK |
4 |
9WTS |
4 |
/GNX |
30 |
EY5V |
| 5 |
ZZZZ |
5 |
T72Y |
5 |
VLDZ |
5 |
NEJ6 |
31 |
LMQS |
| 6 |
GGGG |
6 |
/TDF |
6 |
GXHO |
6 |
9745 |
32 |
C6RR |
| 7 |
NNNN |
7 |
QCHL |
7 |
29LD |
7 |
GUE8 |
33 |
SQC/ |
| 8 |
5555 |
8 |
8DWP |
8 |
SG/I |
8 |
QN1K |
34 |
/K61 |
| 9 |
YYYY |
9 |
ZV7N |
9 |
YQRF |
9 |
71SV |
35 |
0NI7 |
| 0 |
WWWW |
0 |
E/87 |
0 |
3M2V |
0 |
4SAG |
36 |
WHOW |
CHECK CALL: 5 Q O U - A B C D
NATO CONFIDENTIAL ORIGINAL 29
|